Security Policies:

Security Policies:
The security team is committed to keeping Out Of The Blue platform safe and secure, in addition to ensuring that customer’s data is protected. We are focused on all aspects of security, which include
Physical security
Network security
Data Security
Systems Security (Platform, Application and IAM infrastructure)
We recognize that it is equally important to restore service, in case of any issues. This is clarified as part of our Availability & Disaster Recovery Procedures available at
Backup Policies
Disaster Recovery Policies
Physical Security
Out Of The Blue Platform utilizes ISO 27001 and FISMA certified data centers managed by Amazon. Amazon has many years of experience in designing, constructing, and operating large-scale data centers. This experience has been applied to the AWS platform and infrastructure. Physical access is strictly controlled both at the perimeter and at building ingress points by professional security staff utilizing video surveillance, state of the art intrusion detection systems, and other electronic means. Authorized staff must pass two-factor authentication no fewer than three times to access data center floors. All visitors and contractors are required to present identification and are signed in and continually escorted by authorized staff. Amazon only provides data center access and information to employees who have a legitimate business need for such privileges. When an employee no longer has a business need for these privileges, his or her access is immediately revoked, even if they continue to be an employee of Amazon or Amazon Web Services. All physical and electronic access to data centers by Amazon employees is logged and audited routinely.
For additional information see: AWS Security
Network Security
Firewalls
Firewalls are utilized to restrict access to systems from external networks and between systems internally. By default all access is denied and only explicitly allowed ports and protocols are allowed based on business need. Each system is assigned to a firewall security group based on the system’s function. Security groups restrict access to only the ports and protocols required for a system’s specific function to mitigate risk.Host-based firewalls restrict customer applications from establishing localhost connections over the loopback network interface to further isolate customer applications. Host-based firewalls also provide the ability to further limit inbound and outbound connections as needed.
DDOS Mitigation
Our infrastructure provides DDoS mitigation techniques including TCP Syn cookies and connection rate limiting in addition to maintaining multiple backbone connections and internal bandwidth capacity that exceeds the Internet carrier supplied bandwidth. We work closely with our providers to quickly respond to events and enable advanced DDoS mitigation controls when needed.
Spoofing & Sniffing Protections
Managed firewalls prevent IP, MAC, and ARP spoofing on the network and between virtual hosts to ensure spoofing is not possible. Packet sniffing is prevented by infrastructure including the hypervisor which will not deliver traffic to an interface which it is not addressed to. Emotive utilizes application isolation, operating system restrictions, and encrypted connections to further ensure risk is mitigated at all levels.
Port Scanning
Port scanning is prohibited and every reported instance is investigated by our infrastructure provider. When port scans are detected, they are stopped and access is blocked.
Data Security
Customer data is stored in separate access-controlled databases per application.
Database access is limited to specific staff from white-listed IPs only
System Security
System Configuration
System configuration and consistency is maintained through standard, up-to-date images, configuration management software, and by replacing systems with updated deployments.Systems are deployed using up-to-date images that are updated with configuration changes and security updates before deployment. Once deployed, existing systems are decommissioned and replaced with up-to-date systems.
System Authentication
Operating system access is limited to Out Of The Blue staff and requires username and key authentication. Operating systems do not allow password authentication to prevent password brute force attacks, theft, and sharing. All important systems need Multi-Factor Authentication.
Vulnerability Management
Our vulnerability management process is designed to remediate risks without customer interaction or impact. Out Of The Blue is notified of vulnerabilities through internal and external assessments, system patch monitoring, and third party mailing lists and services. Each vulnerability is reviewed to determine if it is applicable to Out Of The Blue’s environment, ranked based on risk, and assigned to the appropriate team for resolution.
Third-Party Audit
AWS undergoes various third-party audits on a regular basis and can provide verification of compliance controls for its data centers, infrastructure and operations.
Backups
Application Databases
All of the application data is fully snapshotted every 24 hours. Out Of The Blue can restore data from the last snapshot and/or incremental backup if data loss occurs.
Application Configuration
All of the application configuration is snapshotted every 24 hours. Out Of The Blue can restore configuration from the last snapshot if data loss occurs. Manual configuration backups performed with every major change to Out Of The Blue infrastructure.
Disaster Recovery
Application Databases & Configuration
Our platform automatically restores customer applications and databases in the case of an outage.
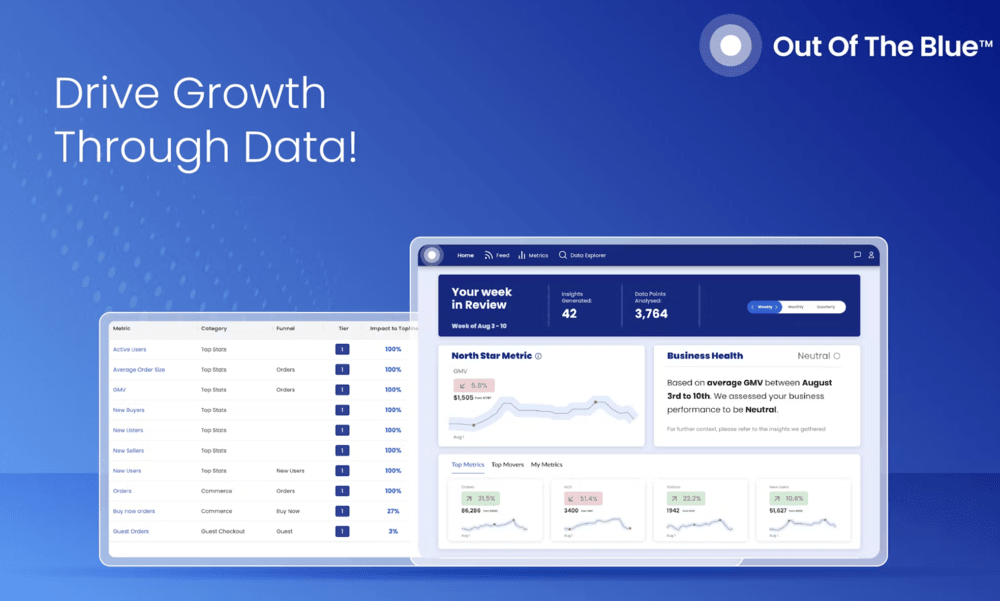
Step into the future of eCommerce.
Learn how we can help your brand drive top-line revenue growth and fix revenue leakage